NO!! This is not this kind of farm neither!
Background story (that you can safely ignore)
One of my side gigs is at a 501(c)(3) Non-profit organization. It is never easy for Non-profit and we are always trying to save a few bucks here and there. We have been using Quickbooks online to deal with our accounting needs, but that is costing more than $1,000 a year. In searching for a cheaper solution, here is a guide created for this purpose and probably could save us that $1,000 each year. But you can use this guide to setup RDWeb for your home lab or any company.
If you are willing to sacrifice speed and performance, this setup can be free for the first year and then less than $50 the years follow. (As long as AWS does not increase their prices) (To keep it free, you will probably need to shut down the servers during off business hours to keep the usage within the 750 hours /month limit) On the other hand, if you have the 501(c)(3) status, you can join Techsoup.org and get products/services at a discounted price. Upgrading to Techsoup Boost (for the price of $79 / year) will get you Quickbooks Premier 2019 for free, as well as a bigger discount on AWS credits. You can get $2,000 AWS credit for just $80. Techsoup Boost sent me a $25 promo code to use for my first purchase, making it $79 + $80 – $25 = $134 for this whole setup, and I can use the $2,000 credits to size up my instances on AWS.
I am setting up RDWeb to launch Quickbooks to make it easier for our accountant to access the desktop version. For RDweb, we will also need to purchase 1 RDS CAL license if we end up going with this approach. Another option is to have them RDP to the AWS instance directly. If that’s the case, you can just get a AWS workspace instance and install Quickbooks Desktop version there. If you do not mind the RDP approach, it will give you a bigger saving / better performance if you just use a single instance of AWS workspace.
Requirements:
- AWS account. You can register for a free tier, and apply the $2,000 AWS credit. (if you are a nonprofit)
- 3 windows EC2 instances. I built my environment with the free tier (t2.micro with 30 GB of storage). I will probably resize the Session host for better performance.
- A 3rd party SSL Certificate (I did not get this)
- RDS CAL Licenses
This is part 2 of the RDWeb Farm Deployment Guide. You should have everything from Part 1 ready before starting this guide.
We will start by opening Server manager on TESTRD01 and going back to our Remote Desktop Services -> Collection page. Right click on “tasks” on the upper right corner and choose “Create Session Collection”

Give this collection a name. We will call this collection “RDTEST-Web”.

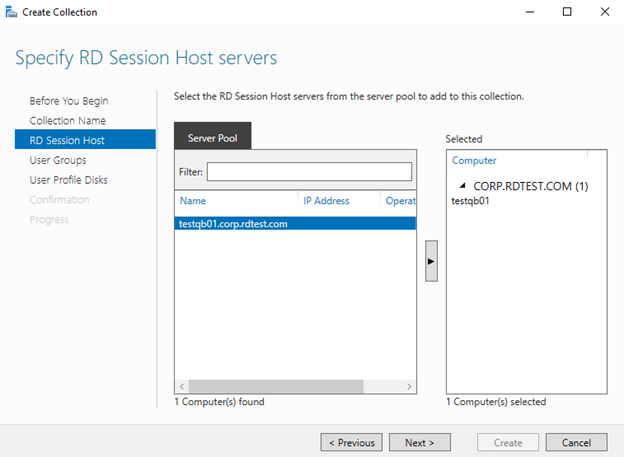
Choose a Session Host server to add to this collection. Since we only have one session host server TESTQB01, we will add that to the right and click “Next”. (If we have a different session host servers that will be hosting a special app that is not installed in other session host, we will need to create a separate collection for that app.)
Here, you can specify which User Groups can have access to the RemoteApp collection. You can either leave it with all members of the Domain Users group (that’s everyone from the Corp.rdtest.com domain) or you can create a security group to restrict access to only certain people.

We will not deal with User Profile Disks in this guide, so un-check “Enable User Profile Disks”.

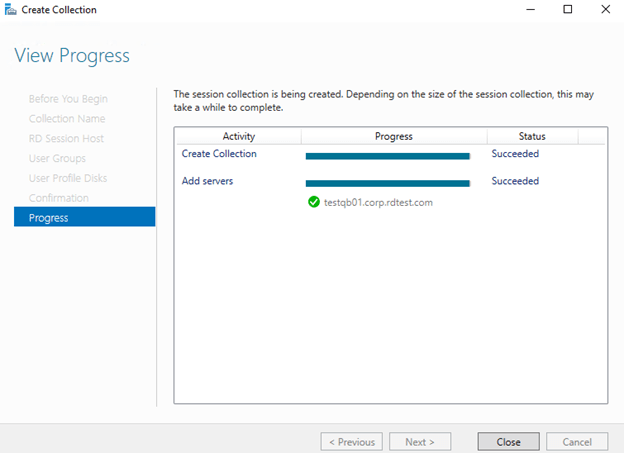
Let the wizard create the collection. It will change the status to Succeeded.
We now have our “RDTEST-Web” displaying under “Collection”.

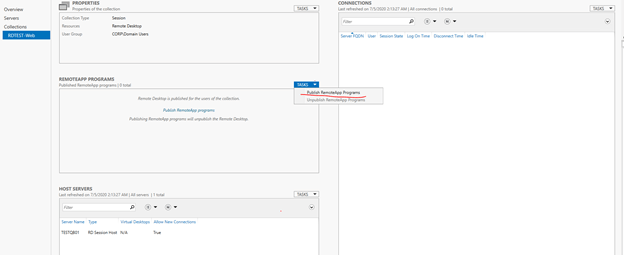
Click on “RDTEST-Web” and click on “tasks” in the middle pane under “RemoteApp Programs” and choose to “Publish RemoteApp Programs”
Pick the RemoteApp that you wish to publish. I will select “Calculator” and “Paint” for the purpose of this guide. You can also click on “Add” to add more apps to the list.

Confirm and publish the apps.

You now see the newly published Apps under “RemoteApp Programs”

If you want only certain groups to access to Calculator, and other groups to access Paint, you can change the permission in the properties.


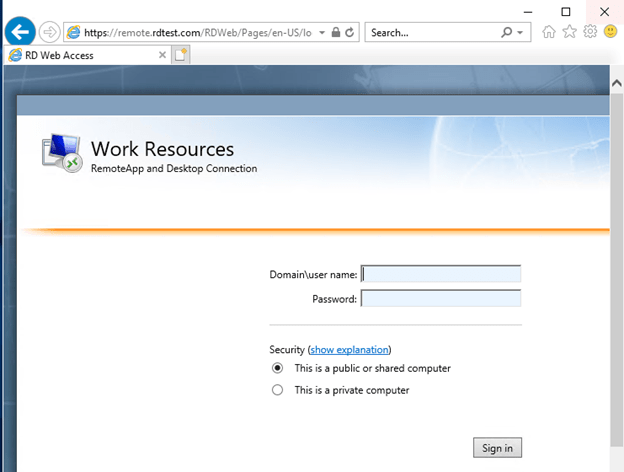
Now, if we go to TESTDC01 and open up an internet explorer, we will be able to access the RDWeb page. (any browser will do) Type in https://testrd01.corp.rdtest.com/RDweb and you will be directed to the login page.
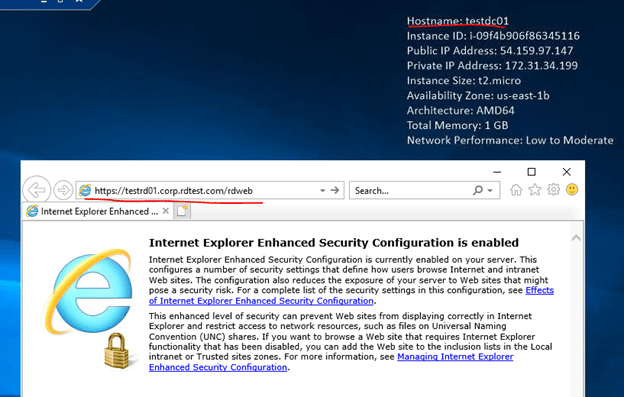
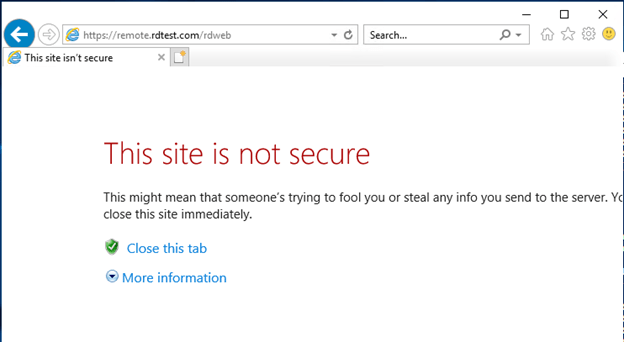
You will see this page “This site is not secure” because we have not install the self-signed SSL on TESTDC01 yet. We can click on “more information” and go on to the webpage to access it for the time being.

Type in your domain user name and password

WooHoo! we are in and both Calculator and Paint are here.

Click on the app and you will be prompted to open or save the RDP file. Open the file.

Calculator is launching! This setup is working as expected internally now.

Currently, we are typing in the FQDN to access the page. It could be a security concern because everyone will know the name of our Connection Broker. We will now work on hiding that name. This will also make it easier for user to remember.
Now that we are still on TESTDC01, open up DNS Manager. Under “Forward Lookup Zones”, right click and select to add “New Zone”

We only have a single Domain Controller for this setup, so any option will do. In case if you are setting this up for your company, you can choose to replicate this zone to all DNS servers in the forest or in the domain, depending on how you plan on using the RDWeb.

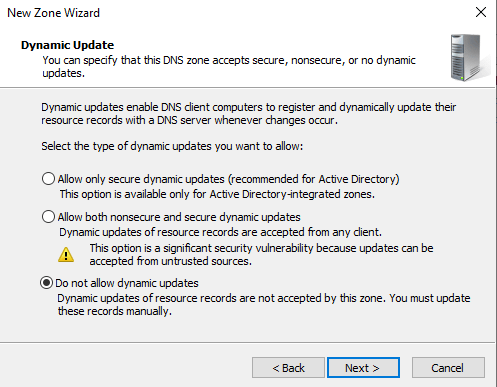
We will name this zone “remote.rdtest.com”


After the zone is created, right click on the zone and add a “New Host (A or AAAA)”

We will point this A record to the private IP of TESTRD01.

This new forward lookup zone will allow internal user to use https:/remote.rdtest.com/rdweb to access the RDWeb page instead of typing in the FQDN.
There are two more things we will do for internal users to make the whole process easier.
- Redirect any traffic to remote.rdtest.com to the RDWeb page, so that users only require to type in remote.rdtest.com as the URL and do not need to add the /RDWeb at the end.
- Distribute the self-signed SSL to all client machines so that they can bypass that “this page is not seucre” message and go striaght to the login page.
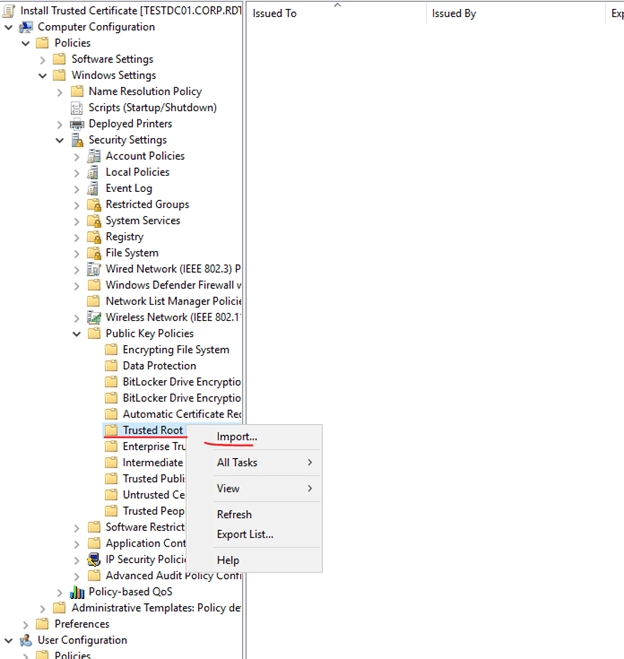
Since we are still on TESTDC01, we will work on distributing that self-signed SSL first. Open up Group Policy Manager. You will need to create a Group Policy Objects. You can either go to an OU and right click to create new Group Policy Object and link it to this OU, or go to Group Policy Objects to create the Policy there first, and then link it to all the OU that require this SSL.

The setting is under Computer configuration -> Policies -> Windows Settings -> Security Settings -> Public Key Policies. Once there, right click on Trusted Root Certification Authorities and select “Import”.

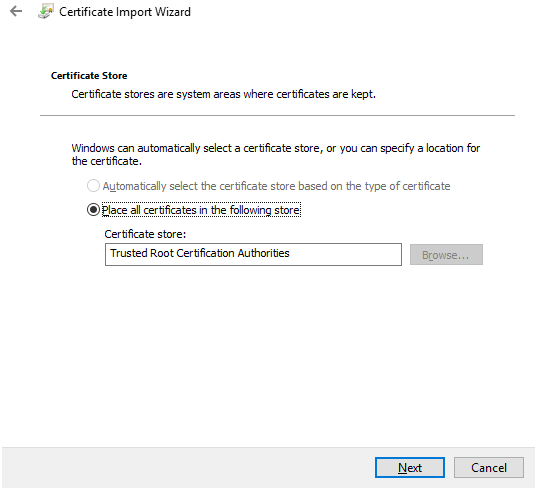
Choose the location of the .pfx file to be imported. You may need to change the file extension before you can see this file.

Type in the password to initiate the import. You should always un-check “Mark this key as exportable” so users cannot export the key and use it elsewhere. If the key is exportable, it may create a security concern.

Make sure it will place it under the “Trusted Root Certification Authorities” Store.
run a gpupdate /force on the client machine and try again. (in my case, I ran gpupdate /force on TESTDC01.) You should no longer see that “this page is not secured” message on any internal client machine that has this policy applied.
Now, go back to the Connection Broker TESTRD01 and run IIS Manager. Go to the “Default Web Site” and go to “HTTP Redirect”
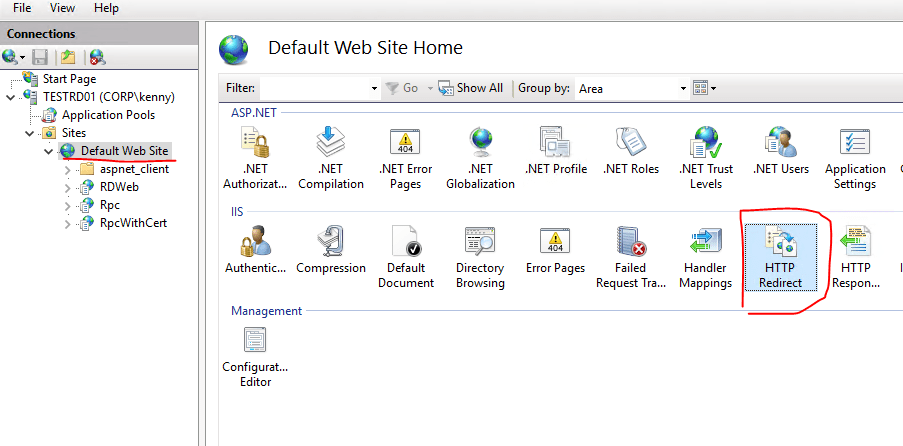
Check the box to “Redirect requests to this destination” and put in “/RDWeb” and make sure the box “Only redirect requests to content in this directory” is checked.
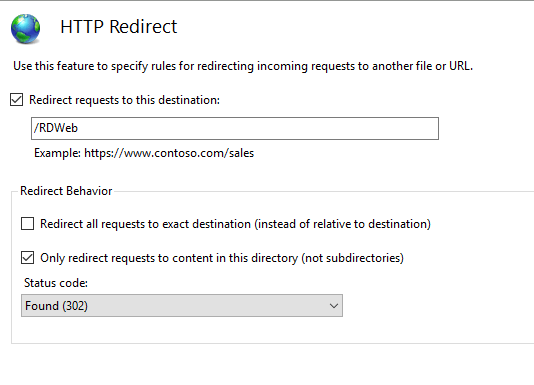
You should always do a iisreset after making changes in IIS Manager to make sure the new settings take effect. Run iisreset in an elevated CMD or Powershell. (Right click to run them as administrator)

If you try to browse to remote.rdtest.com now, it will automatically direct your traffic to the RDWeb page.

Your setup for internal user should now be completed. If you allowed HTTPS traffic to TESTRD01 on AWS, you can now also connect from your home machine if you put in the Public IP of TESTRD01. We will work on access for external client in Part 3 of this guide.

